The most distinct feature of Public Key Infrastructure (PKI) is that it uses a pair of keys to achieve the underlying security service. The key pair comprises of private key and public key.
Since the public keys are in open domain, they are likely to be abused. It is, thus, necessary to establish and maintain some kind of trusted infrastructure to manage these keys.
Key Management
It goes without saying that the security of any cryptosystem depends upon how securely its keys are managed. Without secure procedures for the handling of cryptographic keys, the benefits of the use of strong cryptographic schemes are potentially lost.
It is observed that cryptographic schemes are rarely compromised through weaknesses in their design. However, they are often compromised through poor key management.
There are some important aspects of key management which are as follows −
- Cryptographic keys are nothing but special pieces of data. Key management refers to the secure administration of cryptographic keys.
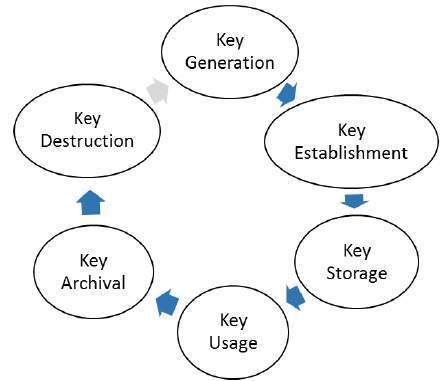
- Key management deals with entire key lifecycle as depicted in the following illustration −
- There are two specific requirements of key management for public key cryptography.
- Secrecy of private keys. Throughout the key lifecycle, secret keys must remain secret from all parties except those who are owner and are authorized to use them.